
Nintendo Switch Hidden Gems: 5 Underrated Games for 2025
The Nintendo Switch boasts a vast library, and while blockbusters get attention, numerous Nintendo Switch hidden gems offer unique and unforgettable experiences that every player should explore in 2025.

Optimize Your Nintendo Switch Storage: MicroSD Card Guide
Effectively optimizing your Nintendo Switch storage is crucial for an uninterrupted gaming experience, primarily achieved by strategically adding a high-capacity microSD card to accommodate your growing digital game library and save data.

PlayStation Accessibility Features: Enhance Your PS5 Gaming
PlayStation accessibility features on PS5 allow gamers to tailor visual, audio, and control settings, ensuring a more inclusive and personalized gaming experience for everyone, regardless of ability.

Secret Tweaks: Unlock Hidden Graphics for Smoother PC Gaming in 2025
Unlocking hidden graphics settings and implementing secret tweaks can dramatically improve your PC gaming experience in 2025, leading to smoother frame rates and superior visual fidelity.

PSN Security Alert: Enable Two-Factor Authentication Now
Activating two-factor authentication (2FA) is paramount for safeguarding your PlayStation Network (PSN) account against unauthorized access and potential hacking attempts, providing an essential extra layer of security beyond just a password.
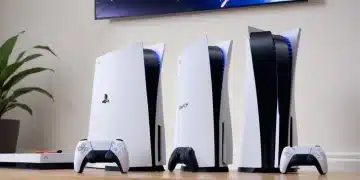
PS5 Models: Choosing the Right PlayStation 5 Console
This article delves into the core distinctions between the various PlayStation 5 models, guiding you through their features, storage options, and design variations to help you select the ideal console for your gaming preferences and budget.




