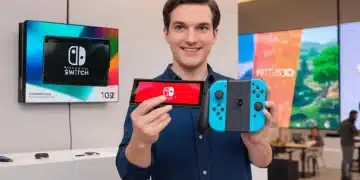
Trade-In Your Old Nintendo Switch: Get Up to $150 Credit for OLED
Maximize your gaming upgrade by learning how to successfully trade-in your old Nintendo Switch for up to $150 credit towards the stunning new OLED model. This guide covers everything from eligibility to best practices for securing top value.

Best PC Gaming Keyboards of 2025: Find Your Perfect Mechanical Keyboard
Finding the best mechanical gaming keyboard in 2025 involves navigating a diverse market of switches, layouts, and features, crucial for optimizing your PC gaming experience with precision and comfort.

PS5 Streaming: Broadcast 4K Gameplay on Twitch and YouTube
Broadcasting your PS5 gameplay in 4K on platforms like Twitch and YouTube requires specific setup and optimization, ensuring high-quality visuals and smooth performance to captivate your audience and elevate your content creation.

PC Game Mods: Enhance Your Favorite Games in 2025
PC game mods are poised to redefine gaming in 2025, offering players unprecedented ways to customize, enhance, and extend their favorite titles with new content, features, and visual improvements created by a passionate global community.

God of War Ragnarök DLC: First Look & Holiday Release
The highly anticipated new God of War Ragnarök DLC, a PlayStation exclusive, is slated for release this holiday season, promising fresh narrative arcs, expanded gameplay, and deeper insights into the Norse saga's beloved characters.

Maximize Nintendo Switch Battery Life: 5 Pro Tips for 2025
To maximize Nintendo Switch battery life for extended play in 2025, optimize system settings, manage screen brightness, disable unnecessary features, utilize power-saving modes, and understand battery health maintenance.




